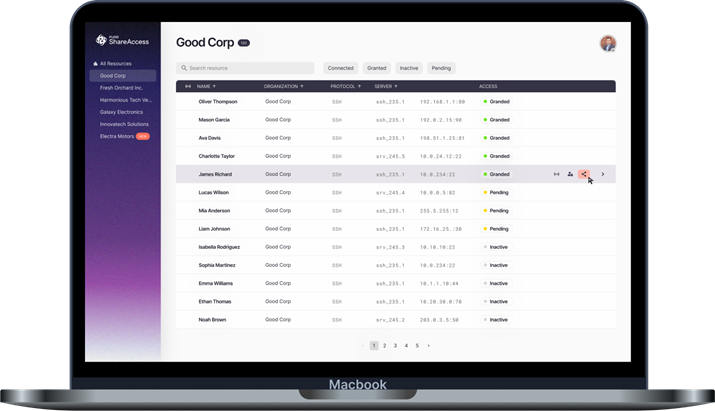
Fudo ShareAccess is a platform that enables enterprises to instantly and securely share privileged resources with third-parties. Designed for secure access, it ensures fast, controlled, and hassle-free vendor collaboration without compromising security.
- Instantly invite external users while maintaining full control over their access permissions.
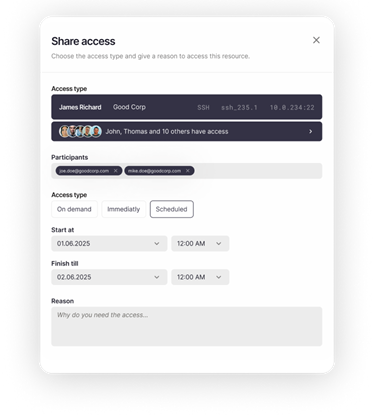
- Set up a tiered approval process for stronger security governance — or use a one-step process for faster turnaround.
- Access is streamlined, yet remains fully secure, ensuring that external users only receive precisely the level of access required, for exactly the time needed.
- Web-based access through a single-click browser interface
- Native support for SSH and RDP protocols
- No need to set up additional VPNs, firewalls, or complex MFA configurations
- Each contractor or vendor receives a defined access scope, eliminating credentials misuse and unauthorized access risks.
- JIT-based access policies ensure that users only receive access when needed and for a strictly limited timeframe —reducing attack surface risks.
- Automated expiration and revocation prevent forgotten or lingering permissions.
Fudo ShareAccess enables enterprises to grant instant, seamless, and policy-enforced access to critical systems.
and Third-Party Onboarding
Manage access across multiple enterprises from one simple portal, giving third parties a single platform to handle access management and simplify collaboration.
Get immediate entry to required resources with no VPN hassles, eliminating complex credential management. and keeping every action logged for transparency and compliance.
Contractors can request and delegate access to shared assets without continuous enterprise admin involvement, ensuring auditable, and policy-compliant provisioning.
Secure access to privileged resources, with customizable deployment options to ensure scalability without risk to sensitive information.
Discover a revolutionary approach to external access management. Request a demo and learn how Fudo ShareAccess enables secure, controlled, and efficient collaboration with external vendors and contractors.