
The European Union’s Digital Operational Resilience Act (DORA) is set to reshape the financial sector’s approach to operational resilience. With enforcement beginning January 17, 2025, financial entities and critical ICT third-party providers must prioritize DORA compliance or face significant repercussions.
Key Takeaways for the Financial Sector:
- Financial Organizations found in breach face fines reaching a staggering €10 million or 2% of their annual global turnover. EOs, CFOs, and other responsible parties can be personally fined up to €1 million.
- Critical ICT providers face even harsher penalties. Fines can reach €5 million or 1% of average daily worldwide turnover, with individuals facing fines up to €500,000.
- Strengthening the capabilities of ICT risk management, incident reporting, and third-party risk management are required to comply with DORA.
Digital Operational Resilience Act (DORA) Framework for the EU Financial Entities
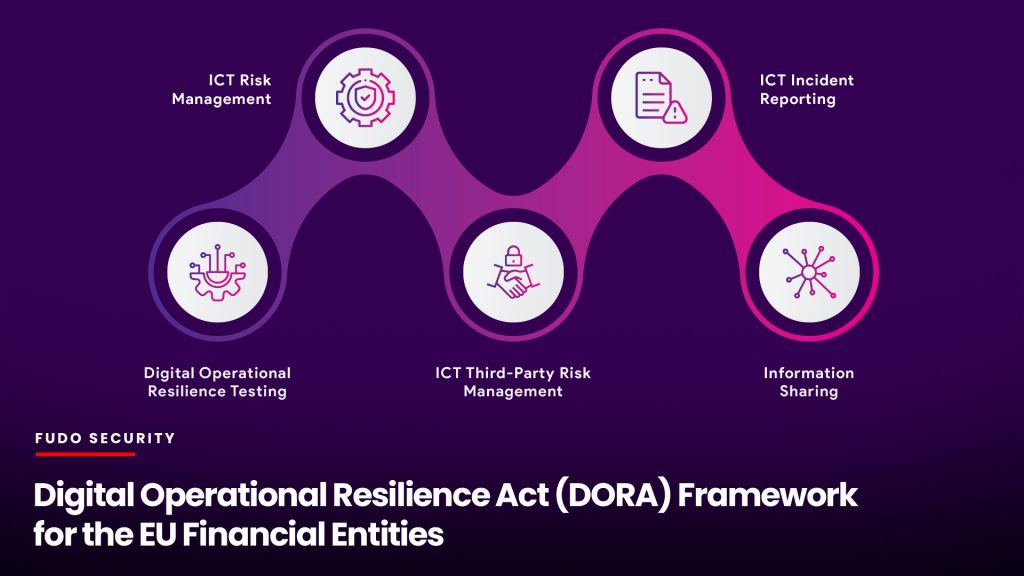
The Digital Operational Resilience Act (DORA) establishes a comprehensive regulatory framework for managing Information and Communication Technology (ICT) risks within the financial sector. It encompasses five key pillars:
ICT Risk Management: Requires implementing an ICT risk management framework to identify, assess, and mitigate potential risks, including cyberattacks, system failures, and human error.
ICT Incident Reporting: Mandates establishing clear procedures for reporting ICT-related incidents to relevant authorities, ensuring transparency and timely response.
Digital Operational Resilience Testing: Requires regular testing, including stress tests and scenario analysis, to evaluate the resilience of critical systems to disruptions.
ICT Third-Party Risk Management: Sets stringent guidelines for managing risks associated with outsourcing critical ICT services to third parties.
Information Sharing: Encourages collaboration and information sharing among financial entities to enhance collective awareness and response to cyber threats.
ICT Risk Management: Building a Foundation for Resilience of Financial Entities
DORA compliance requires the implementation of a comprehensive ICT risk management framework. This framework should be a living document, regularly reviewed and updated to reflect the evolving threat landscape. It should include:
Risk identification
A systematic process for identifying potential ICT risks, including cyber attacks, system failures, human error, and third-party risks. This could involve threat modeling, vulnerability scanning, and risk assessments.
Example: A bank might identify the risk of a DDoS attack disrupting its online banking services or the risk of a data breach resulting from a phishing attack targeting employees.
Risk assessment
A methodology for evaluating the likelihood and impact of identified risks. This could involve qualitative assessments, quantitative analysis, or a combination of both.
According to a 2023 report by the European Central Bank, cyber incidents are the most significant source of operational risk for financial institutions, with an average annualized loss of €1.5 million per institution.
Risk mitigation
Strategies and controls to reduce the likelihood and impact of ICT risks. This could include security measures such as firewalls, intrusion detection systems, and encryption, as well as operational controls such as data backups and disaster recovery plans.
Example: A financial institution might implement multi-factor authentication to mitigate the risk of unauthorized access to critical systems.
ICT Incident Reporting: Transparency and Timely Response to Cyber Threats in the Financial Sector
DORA requires financial entities to establish clear procedures for reporting ICT-related incidents to relevant authorities. This includes:
Defining reportable incidents
Clear criteria for determining which incidents must be reported, including their severity, impact, and potential for systemic risk. For example, DORA requires reporting of major ICT-related incidents, which are incidents that have a significant impact on the financial entity’s operations, financial performance, or reputation.
Establishing reporting channels
Designated channels for reporting incidents to relevant authorities, such as national competent authorities or the European Supervisory Authorities (ESAs).
Timely reporting is also in scope, which requires specific timeframes for reporting incidents, ensuring that authorities are informed promptly to facilitate a coordinated response. According to a 2022 survey by the European Banking Authority, 44% of banks experienced at least one major ICT incident in the previous year.
Digital Operational Resilience Testing: Ensuring Preparedness of Financial Entities to Cyber Attacks
DORA compliance requires regular testing to evaluate the resilience of critical systems to disruptions. This includes:
Stress Testing Against Cyber Attacks
Simulating extreme conditions, such as high transaction volumes or cyberattacks, to assess system performance and identify vulnerabilities. For example, a payment processor might simulate a DDoS attack to test the resilience of its payment processing systems.
Scenario analysis
Evaluating the impact of various disruption scenarios, such as natural disasters or pandemics, on critical business processes. For example, an investment firm might analyze the impact of a prolonged power outage on its trading operations.
DORA compliance also requires regular testing frequency: it should be conducted at least annually or more frequently to enable better ICT risk management for financial entities with higher ICT risk profiles.
ICT Third-Party Risk Management: Due Diligence and Oversight
DORA sets stringent guidelines for managing ICT third-party risk. This includes:
Due diligence
A thorough assessment of the security posture and operational resilience of third-party providers before engaging their services. For example, a bank might require a third-party cloud provider to demonstrate compliance with relevant security standards and undergo independent audits.
Contractual obligations
Clear contractual agreements with third-party providers that define security and resilience requirements, service level agreements, and incident response procedures.
Ongoing monitoring
Continuous monitoring of third-party providers to ensure they maintain compliance with DORA requirements and contractual obligations. A 2023 report by the Ponemon Institute found that 59% of organizations experienced a data breach caused by a third party.
Information Sharing: Collective Defense Against Cyber Threats
DORA compliance requires financial entities to collaborate and share information among financial entities to enhance collective awareness and response to cyber threats. This includes:
Threat intelligence sharing
Sharing information about emerging threats, vulnerabilities, and attack patterns. For example, financial institutions can participate in industry-specific information sharing and analysis centers (ISACs) to exchange threat intelligence.
Incident response coordination
Collaborating on incident response efforts to contain and mitigate the impact of cyberattacks.
Best practice sharing
Sharing best practices for ICT risk management, incident response, and operational resilience. For example, Financial institutions can participate in industry forums and workshops to learn from each other’s experiences and improve their security posture.
The Consequences of Non-Compliance with Digital Operational Resilience Act
Non-compliance with the Digital Operational Resilience Act (DORA) carries significant financial and operational consequences. Organizations face potential fines of up to €10 million or 2% of their annual global turnover, whichever is greater. Furthermore, continued non-compliance can result in daily penalties of 1% of average daily worldwide turnover.
Individual accountability is a key aspect of DORA. CEOs, CFOs, and other responsible individuals within these organizations can be personally fined up to €1 million. This highlights the importance of strong leadership and a culture of compliance.
Critical ICT third-party providers face even stricter penalties, with fines reaching €5 million or 1% of average daily worldwide turnover and individual fines of up to €500,000.
Beyond financial penalties, non-compliance exposes organizations to operational disruptions, reputational damage, and potential legal action.
ICT Risk Management and DORA Compliance Can Save Money
While DORA enforcement actions are still to emerge, the General Data Protection Regulation (GDPR) provides a valuable example of the consequences of non-compliance.
In 2020, British Airways was fined £20 million for a data breach affecting over 400,000 customers. This case illustrates the seriousness with which regulators approach data security and operational resilience.
PAM for Digital Operational Resilience Act Compliance: ICT Risk Management at its Core
Privileged Access Management (PAM) plays a major role in achieving and maintaining DORA compliance. By implementing a comprehensive PAM solution, organizations can effectively address several key requirements of the regulation.
How PAM Supports DORA Compliance and ICT Risk Management
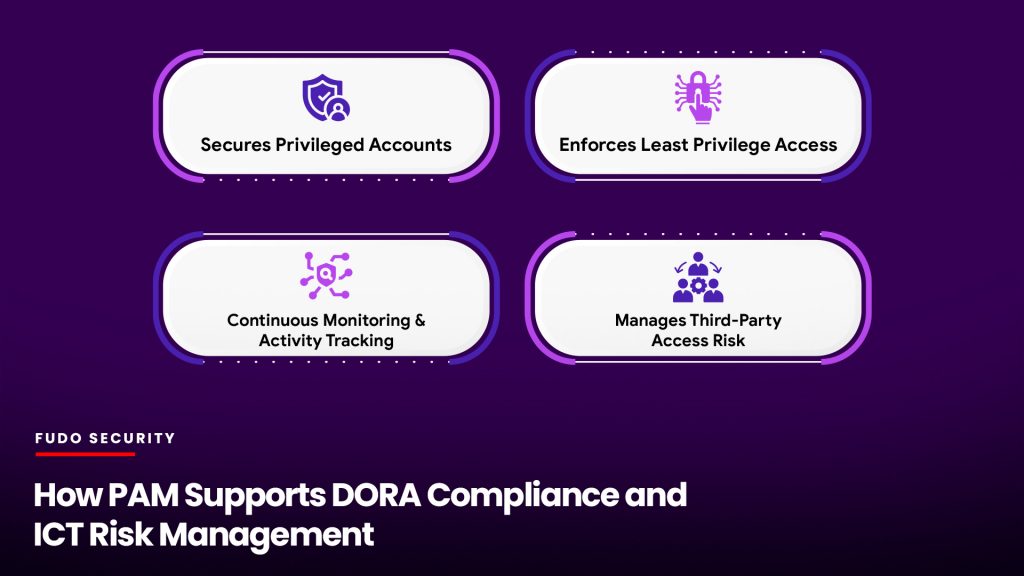
Securing Privileged Accounts
PAM safeguards privileged accounts by enforcing strong authentication, controlling access requests, and monitoring privileged activity. This helps mitigate the risk of unauthorized access and data breaches, a key concern under DORA.
Enforcing Least Privileged Access Management
PAM enforces the principle of least privilege, ensuring that users have only the access they need to perform their duties. This minimizes the potential damage from compromised accounts and insider threats.
Continuous Monitoring
PAM provides continuous monitoring of privileged access and activity, enabling real-time detection of suspicious behavior and facilitating incident response. This supports DORA’s requirements for ICT incident reporting and incident management.
Third-Party ICT Risk Management
PAM helps organizations manage ICT third-party risk by providing visibility into the security practices of third-party providers and ensuring they meet DORA’s requirements.
Implementing PAM for DORA Compliance
To effectively leverage PAM, organizations should consider the following steps:
Conduct a Thorough Risk Assessment: Identify and assess all ICT risks, including those related to privileged access.
Implement a Comprehensive PAM Solution: Select a PAM solution that aligns with DORA requirements and addresses the specific needs of the organization.
Integrate PAM with Existing Frameworks: Integrate PAM with existing security and risk management frameworks to ensure a holistic approach to compliance.
Establish Clear Policies and Procedures: Develop clear policies and procedures for managing privileged access, including access requests, approval workflows, and incident response.
Conduct Regular Training and Awareness Initiatives: Educate employees about the importance of privileged access management and DORA compliance.
PAM: A Strategic Investment for Financial Institutions
DORA presents a significant challenge but also an opportunity. By proactively addressing DORA requirements and implementing a comprehensive PAM solution, organizations can mitigate cyber threats, ensure business continuity, and maintain operational resilience in the face of increasing challenges.
Investing in PAM solutions such as FUDO ENTERPRISE not only helps financial institutions achieve DORA compliance but also strengthens their overall security posture, reduces operational risks, and protects their reputation.

